 HOWTO Covers:
HOWTO Covers: Installation of
Moblock on R5.5.
Background Material: MoBlock, like PeerGuardian, blocks internet traffic based on large lists of IP address ranges in order to protect your privacy. The thought is that the blocklists contain IP ranges of hostile people/organizations who could potentially harm you, snoop your PC, log what you're up/downloading, etc.
You can select the level of protection offered by Moblock though your choice of blocklists. Moblock will compile as many as you want into a single file that it uses along with IPtables. It also have a very small memory/CPU footprint.
In order to get this to work on R5.5, you'll need to recompile your kernel with some netfilter support that wasn't selected in the original R5.5 kernel. It's easy, don't worry.

As the topic suggests, these instructions are for R5.5. Do not follow them verbatim on any other release of KM!
Table of Contents:
Section 1. Recompile the needed support into your kernel
Section 2. Install Moblock
Section 3. Appendix - optional - Instructions to configure your kernel if you don't wanna download my pre-made .config
Section 4. References
As always, commands that are preceded by the $ prompt are done by the user (i.e. mythtv) and those preceded by the # prompt are done by root.
 Part 1. Recompile the needed support into your kernel
Part 1. Recompile the needed support into your kernel
First get the kernel-source:
Code:
$ wget ftp://knoppmyth.net/R5/linux-source-2.6.23-chw-4_2.6.23-chw-4-10.00.Custom_all.deb
Untar the source and copy over the R5.5 kernel's out-of-the-box configuration:
Code:
# dpkg -i linux-source-2.6.23-chw-4_2.6.23-chw-4-10.00.Custom_all.deb ; cd /usr/src ; tar xjvf linux-source-2.6.23-chw-4.tar.bz2 ; cd linux-source-2.6.23-chw-4 ; cp /boot/config-2.6.23-chw-4 .config
In case something unforeseen goes wrong, let's backup and setup your current kernel as a backup option for you to boot into, just to be safe. I recommend that you do NOT skip this step.
Code:
# cp /boot/vmlinuz-2.6.23-chw-4 /boot/backup ; cp /boot/initrd.gz /boot/backup.gz
Edit
/etc/lilo.conf using your fav text editor (nano or vim for example). Look for the line that reads: "default=Linux"
Insert the following under it:
Code:
image=/boot/backup
label=Backup
initrd=/boot/backup.gz
read-only
If something goes horribly wrong with our new kernel, when LILO loads, you can hit the down arrow until you highlight "Backup" and boot into your system to fix it

Now we'll compile the kernel with the correct options for moblock to work. The easy way for you to do this is to download my pre-configured .config file (by clicking
here) which contains the needed settings. Rename the file to ".config" and place it in your /usr/src/linux-source-2.6.23-chw-4
Alternatively, manually make the file by following the step-by-step guide located in Section 3 of this post (scroll to the end of the doc).
Do the following:
Code:
# cd /usr/src ; rm linux ; ln -s linux-source-2.6.23-chw-4 linux ; cd /lib/modules/2.6.23-chw-4 ; rm build ; ln -s /usr/src/linux-source-2.6.23-chw-4 build ; cd /usr/src/linux-source-2.6.23-chw-4
Finally do your make steps:
Code:
# make clean
# make -j4
This step took 47 min on a 2.20 GHz Athlon 3200+ w/ 1 gig of DDR2-400, YMMV depending on system configuration. FYI, the -j4 option tells it to use 4 threads. From what I've read, 4 is good for a single core CPU. You can use -j6 or -j8 for a dual core and -f10 or -j12 for a quad core.
Now make your modules, install, and reboot into the new kernel:
Code:
# make modules_install
# make install
(answered yes to re-running lilo)
# reboot
That should be it! You should boot normally except that you'll have the required netfilter kernel support to use moblock.
 Part 2. Install Moblock
Part 2. Install MoblockAdd the following to your /etc/apt/sources.list
Code:
# moblock repos
deb http://moblock-deb.sourceforge.net/debian sid main
deb-src http://moblock-deb.sourceforge.net/debian sid main
Also, verify that you're pointing to the unstable debs (i.e. change the two lines under #Debian repos should contain the word "unstable")
Example:
Code:
# moblock repos
deb http://moblock-deb.sourceforge.net/debian sid main
deb-src http://moblock-deb.sourceforge.net/debian sid main
#Debian repos
deb http://ftp.debian.org unstable main contrib non-free
deb-src http://ftp.debian.org unstable main contrib non-free
Save and exit. Now add the pgp key for moblock's debs to your ring so the authenticity can be verified:
Code:
# gpg --keyserver wwwkeys.eu.pgp.net --recv 9072870B
# gpg --export --armor 9072870B | apt-key add -
Now update apt and install moblock:
Code:
# apt-get update
# apt-get install moblock moblock-control
That'll do it. Once the apt-get finishes, dpkg will run the config for moblock. You can just accept the default options. Switch on or off the blocklists of your choice, see the webpage
here for more info on what all these different lists contain. You likely don't need them all.
It might take 60-120 seconds for the blocklists to update. Just be patient. When finished, moblock automatically starts.
You can control moblock via moblock-control:
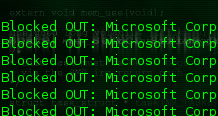
Test that moblock is functional:
Code:
# moblock-control test
Testing MoBlock:
CAUTION: This is just a simple test to check if MoBlock blocks outgoing
connections. For this, an IP from the blocklist will be pinged. Then the test
checks if this IP appears in the logfile /var/log/moblock.log.
MoBlock marks packets to be blocked. This means you have to make sure that the
marked packets are also blocked later (with appropriate iptables rules). If you
are using the default configuration and MoBlock is started after other firewalls
this will be the case.
This test does not check if you have sane iptables rules or if your complete
blocklist is in the correct format. Therefore success doesn't imply that
everything is working as you expect it.
Also have a look at "moblock-control status" and test manually with traceroute.
Trying to ping 4.1.144.255 from /etc/moblock/guarding.p2p ...
MoBlock marked the IP to be blocked and the IP did not answer. Test succeeded.
Stop/restart/start it via the same command (where <command> is one of the preceding):
Code:
# moblock-control <command>
You can add/remove additional blocklists by editing your
/etc/moblock/blocklists.list file.
You can really do everything you need with the console app (moblock-control), so don't feel like you have to install the GUI. If however, you'd prefer a GUI to moblock, install mobloquer like this:
Code:
# apt-get install mobloquer
Once apt-get finishes, you can launch it simply by typing:
Code:
# mobloquer

Note: for the logging feature to work, you need to have mobloquer running 24/7 (or at least over the time period you're interested in seeing). If you have the fluxbox toolbar set to visible, I'd recommend that you have mobloquer launch with fluxbox in tray mode. That way it's hidden from view, but you will benefit from the logging features.
To do this, simply edit your
~/.fluxbox/apps adding the following line:
Code:
[startup] {/usr/bin/mobloquer --tray}
This causes mobloquer to startup silently in the tray when fluxbox starts. You can exit mythtvfrontend, and can look at mobloquer via the tray icon and it's always running.

 Appendix - Manually Configuring the Kernel
Appendix - Manually Configuring the KernelDo this from the /usr/src/linux-source-2.6.23-chw-4/
Code:
# make menuconfig
After a few seconds, you should be presented with a menu-like view of the kernel options. Navigate with the arrow keys and the ENTER key. You're task is to the select the various options listed below and modify them as follows to took like mine:
Hit the 'Y' key to include and you'll see the character that was present switch to an asterisk (i.e. <*>) when you do so.
Hit the 'N' key to exclude and you'll see it turn to nothing (i.e. < >) when you do it.
Hit the 'M' key to make the option a kernel module. You'll see it change to a capital 'M' when you do so (i.e. <M>).
Start by navigating to the following:
Networking --->
Networking options --->
[*] Network packet filtering framework (Netfilter) --->
Core Netfilter Configuration --->From this section, make your display look like the following. Note that some options won't be displayed until you select them. In other words, go down the list making your window match the text below. You'll note that some additional options are revealed as you make your way down the list:
Code:
x lqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqk x
x x <*> Netfilter netlink interface x x
x x <*> Netfilter NFQUEUE over NFNETLINK interface x x
x x <M> Netfilter LOG over NFNETLINK interface x x
x x <*> Netfilter connection tracking support x x
x x --- Connection tracking flow accounting x x
x x --- Connection mark tracking support x x
x x [ ] Connection tracking security mark support (NEW) x x
x x [ ] Connection tracking events (EXPERIMENTAL) (NEW) x x
x x < > SCTP protocol connection tracking support (EXPERIMENTAL) (NEW) x x
x x < > UDP-Lite protocol connection tracking support (EXPERIMENTAL) (NEW) x x
x x < > Amanda backup protocol support (NEW) x x
x x < > FTP protocol support (NEW) x x
x x < > H.323 protocol support (EXPERIMENTAL) (NEW) x x
x x < > IRC protocol support (NEW) x x
x x < > NetBIOS name service protocol support (EXPERIMENTAL) (NEW) x x
x x < > PPtP protocol support (NEW) x x
x x < > SANE protocol support (EXPERIMENTAL) (NEW) x x
x x < > SIP protocol support (EXPERIMENTAL) (NEW) x x
x x < > TFTP protocol support (NEW) x x
x x <*> Connection tracking netlink interface (EXPERIMENTAL) x x
x x <*> Netfilter Xtables support (required for ip_tables) x x
x x <M> "CLASSIFY" target support x x
x x <M> "CONNMARK" target support x x
x x <M> "DSCP" target support x x
x x <M> "MARK" target support x x
x x <M> "NFQUEUE" target Support x x
x x <M> "NFLOG" target support x x
x x <M> "NOTRACK" target support x x
x x <M> "TRACE" target support x x
x x <M> "SECMARK" target support x x
x x <M> "TCPMSS" target support x x
x x <M> "comment" match support x x
x x <M> "connbytes" per-connection counter match support x x
x x <M> "connlimit" match support" x x
x x <M> "connmark" connection mark match support x x
x x <M> "conntrack" connection tracking match support x x
x x <M> "DCCP" protocol match support x x
x x <M> "DSCP" match support x x
x x <M> "ESP" match support x x
x x <M> "helper" match support x x
x x <M> "length" match support x x
x x <M> "limit" match support x x
x x <M> "mac" address match support x x
x x <M> "mark" match support x x
x x <M> IPsec "policy" match support x x
x x <M> Multiple port match support x x
x x <M> "physdev" match support x x
x x <M> "pkttype" packet type match support x x
x x <M> "quota" match support x x
x x <M> "realm" match support x x
x x <M> "sctp" protocol match support (EXPERIMENTAL) x x
x x <M> "state" match support x x
x x <M> "statistic" match support x x
x x <M> "string" match support x x
x x <M> "tcpmss" match support x x
x x < > "u32" match support x x
x x < > "hashlimit" match support x x
x mqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqj x
That's it for this section. Go back by hitting the ESC key twice, then go into the following section and setup your display to match the text below:
IP: Netfilter Configuration --->From this section, make your display look like the following:
Code:
x lqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqk x
x x <*> IPv4 connection tracking support (required for NAT) x x
x x [*] proc/sysctl compatibility with old connection tracking (NEW) x x
x x < > IP Userspace queueing via NETLINK (OBSOLETE) x x
x x <*> IP tables support (required for filtering/masq/NAT) x x
x x <M> IP range match support x x
x x <M> TOS match support x x
x x <M> recent match support x x
x x <M> ECN match support x x
x x <M> AH match support x x
x x <M> TTL match support x x
x x <M> Owner match support x x
x x <M> address type match support x x
x x <M> Packet filtering x x
x x <M> REJECT target support x x
x x <M> LOG target support x x
x x <M> ULOG target support x x
x x <M> Full NAT x x
x x <M> MASQUERADE target support x x
x x <M> REDIRECT target support x x
x x <M> NETMAP target support x x
x x <M> SAME target support (OBSOLETE) x x
x x <M> Basic SNMP-ALG support (EXPERIMENTAL) x x
x x <M> Packet mangling x x
x x <M> TOS target support x x
x x <M> ECN target support x x
x x <M> TTL target support x x
x x < > CLUSTERIP target support (EXPERIMENTAL) (NEW) x x
x x <M> raw table support (required for NOTRACK/TRACE) x x
x x <M> ARP tables support x x
x x <M> ARP packet filtering x x
x x <M> ARP payload mangling x x
x mqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqj x
That's it for the configuration. Don't mess with any of the other options unless you know what you're doing!
To exit and save the configuration, keep hitting the ESC key until you're asked if you want to save the configuration. Say 'Yes' to that question!
Okay! You just configured your kernel. Now go back up to Part 1 and complete the rest of the process.
 References
References
The following sites are sources for block lists
http://blocklist1.snowmanuk.net/
http://forums.phoenixlabs.org/showthread.php?t=17454
The following links helped me to figure out how to recompile the kernel and to get moblock up and running
http://moblock-deb.sourceforge.net/
http://forums.phoenixlabs.org/forumdisplay.php?f=15
http://gentoo-wiki.com/Moblock
http://www.cyberciti.biz/tips/compiling ... el-26.html
http://knoppmyth.net/phpBB2/viewtopic.php?t=18993
http://knoppmyth.net/phpBB2/viewtopic.php?t=18949
http://knoppmyth.net/phpBB2/viewtopic.php?t=13281
http://knoppmyth.net/phpBB2/viewtopic.php?t=18607


 Print view
Print view
 Previous topic Next topic
Previous topic Next topic 

